INTERNAL PENETRATION TESTING
An Internal Penetration Test evaluates your organization’s internal networks and systems for security vulnerabilities. By simulating real-world cyberattacks from an insider’s perspective, it offers insights into potential threats such as ransomwares.
What you'll get:
- Executive Summary: Outlining risk management implications
- Technical Report: Detailling vulnerabilities in mission critical systems
- Recommendations: Walkthrough on how to fix identified vulnerabilities
- Expert Guidance: Actions plan to improve your internal network security
- Attestation: To meet compliance requirements (SOC2, ISO27001, etc.)
What is Internal Penetration Testing?
Unlike external penetration tests, internal pen testing offers an insider’s perspective. It focuses on what could happen if someone with internal access, such as employees or contractors, tries to exploit vulnerabilities within your organization.
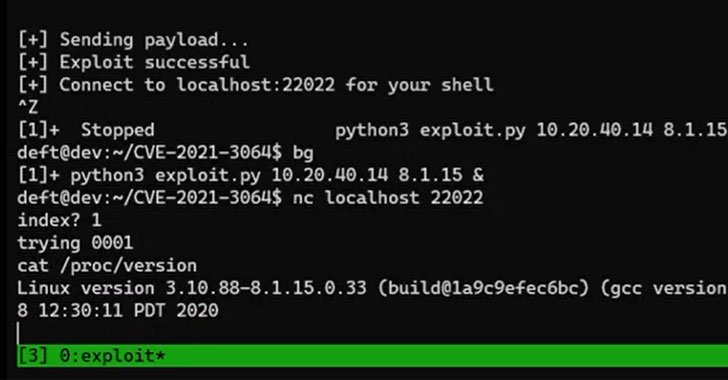
Leveraging tailored strategies, our seasoned cybersecurity experts simulate insider cyber-attacks to identify vulnerabilities in your internal networks, and mission critical systems. This isn’t a checkbox exercise; it’s a rigorous, custom analysis designed to root out vulnerabilities that generic testing might overlook. The goal is to provide a thorough security analysis that uncovers potential internal risk. This enables us to deliver actionable mitigation strategies that will security your internal IT environment against costly cyberattacks such as ransomwarets.
Why Should You Perform an Internal Penetration Test?
- Ransomware Resilience
Internal systems are prime hunting grounds for ransomware attacks, which can paralyze business operations and compromise critical data. - Insider Threat Landscape
Standard security controls often neglect the risks originating from inside the organization, leaving vulnerabilities in internal defenses. - Growing Internal Complexity
The growing interconnectedness of devices and systems compounds the complexity of managing internal vulnerabilities, making a thorough assessment ever more crucial. - Compliance Challenges
Stringent industry regulations increasingly require internal assessments to safeguard data integrity and ensure compliance. - Security Solutions Shortcomings
While conventional security tools may catch routine threats, they are often ill-equipped to defend against sophisticated internal cyberattacks.
How Will Internal Pen testing Help Secure my Internal Network?
-
Protect against ransomware attacks
Safeguard your data and mission-critical systems against costly ransomware cyberattacks.
-
Understand your internal network vulnerabilities
Perform comprehensive internal pen tests to thoroughly assess the security of your networks and assets.
-
Simulate insider threat scenarios
Emulate potential insider threats and vulnerabilities to determine the robustness of your internal network security controls.
-
Benchmark with top security standards
Align your internal security practices with recognized industry standards.
-
Stay updated with the latest security measures
Incorporate the latest security strategies to protect against both internal and external threats.
What Will be Assessed During an Internal Penetration Test?
-
File Servers & Domain Controllers
Evaluating access controls, permissions, and configurations.
-
Active Directory
Analysis of user management, password policies, and more.
-
Network Devices
Evaluating router, switch, and other device configurations.
-
Authentication
Testing across both legacy and contemporary authentication protocols.
-
Data Security
Analyzing permissions, access controls, and encryption standards.
-
And more
Network segmentation, legacy systems, patch management strategies, endpoints, etc.

What are the Benefits of Conducting an Internal Infrastructure Penetration Test?
Internal pen tests are a critical cornerstone in fortifying your organization’s cybersecurity defenses from within.
Mitigated Insider Threats
Lower chances of data breaches and unauthorized insider access by identifying and patching weaknesses.
Regulatory Compliance
Easily meet and maintain security standards, including compliance like SOC 2, PCI-DSS, ISO 27001.
Focused Resource Distribution
Use insights from the pentest to allocate resources strategically, focusing on your network's vulnerable areas.
Enhanced Security for
Critical Assets
Implement controls to protect crucial internal assets like data centers and proprietary software.
Strengthened
Access Control
Optimize user permissions and access controls to minimize unauthorized or unintended access to resources.
Increased
Security Awareness
Gain a detailed understanding of your internal security landscape and keep stakeholders informed.
Got an Upcoming Project? Need Pricing For Your External Penetration Test?
Answer a few questions regarding your needs, project scope and objectives to quickly receive a tailored quote. No engagement.
- You can also call us directly: 1-877-805-7475
Our Internal Penetration Testing Process
New to penetration testing or curious about Vumetric’s unique approach? Our streamlined framework applies to all our services—be it internal pen test or other specialized penetration tests. We’ve broken it down into these crucial steps for clarity and transparency:
Project Scoping
Duration: ~ 1-2 days
Activities: We learn about your specific needs and objectives.
Outcome: Business proposal, signed contract.
Kick-off / Planning
Duration: ~ 1 hour
Activities: We review the scope of work, discuss requirements and planning.
Outcome: Scope validation, test planning.
Penetration Testing
Duration: ~ 2-3 weeks
Activities: We execute the test in accordance with the project scope.
Outcome: Detailed penetration test report, presentation.
Remediation Testing
Duration: Up to 1 month
Activities: We test and validate vulnerability fixes.
Outcome: Remediation report, attestation.
Download The Vumetric Penetration Testing Buyer's Guide
Learn everything you need to know about penetration testing to conduct successful pentesting projects and make informed decisions in your upcoming cybersecurity assessments.

Internal Penetration Testing FAQ
Couldn’t find the information you were looking for? Ask an expert directly.
Industry best practices recommend conducting internal pen tests at least annually to stay ahead of emerging cybersecurity threats. Additional internal testing is especially important in certain situations, such as before deploying new internal systems, after significant changes to the network, before compliance audits, after security incidents, and before significant business events such as mergers and acquisitions. This ensures that your internal network remains resilient to evolving cyber threats.
Our internal penetration testing helps a wide range of organizations meet their compliance goals each year by identifying critical vulnerabilities that require immediate remediation and efficiently meeting compliance standards such as SOC2, ISO27001, PCI-DSS.
The cost of an internal pen test varies greatly depending on the scope of the assessment.One of the key factors affecting the cost is the number of internal systems and endpoints that need to be evaluated.
Learn more about the main factors that determine the cost of a penetration test →
Quickly receive a free quote with no engagement using our streamlined quoting tool →
Our certified penetration testers use globally recognized frameworks, such as the MITRE ATT&CK and OSSTMM testing methodologies, to provide an accurate snapshot of your current external cybersecurity risks that could escalate into an incident.Using a blend of manual and automated techniques, we not only identify vulnerabilities, we contextualize them.This helps our clients effectively allocate their IT and network security resources to protect sensitive data.
Why Choose Vumetric For Internal Penetration Testing?
Proven Methodologies
Our testing methodologies are based on industry best practices and standards.
ExperiencedTeam
Our team of certified experts conducts more than 400 pentest projects annually.
ActionableResults
Discover how our pentest services helped organizations improve security of their internal assets.
Read Our Clients' Success Stories
Discover how our pentest services helped organizations of all types improve the security of their internal networks and servers:
" The report was clearly written, with clear documentation of the problem and with clear explanations for how and why these items should be addressed. We were able to fix all issues and receive confirmations instantaneously. ”
Daniel R, CEO and Chief Scientist
“ They kept us informed during the whole testing process told us what they’d be doing every step of the way. We were quite happy with the results and what they found. We were impressed with their team and consistent communication. ”
Mirko B., Director of Compliance
“ Vumetric conducted internal penetration testing and showed us where we were vulnerable. They made the process smooth, were very responsive and well organized. They really impressed us as specialists in their field. ”
Elizabeth W., General Manager
Featured Network Cybersecurity Resources
Certified Penetration Testing Team
Our experts hold the most widely recognized penetration testing certifications. Partner with the best in the industry to protect your mission critical IT assets against cyber threats.