What is Mainframe Penetration Testing?
A mainframe penetration testing is an assessment that identifies and fixes vulnerabilities within mainframe systems, using the same techniques as hackers to breach your infrastructure.
According to most mainframe manufacturers, such as IBM, it is each user’s responsibility to identify and mitigate mainframe vulnerabilities, whether at the software or hardware level. Mainframe penetration testing allows organizations to uncover any opportunity for hackers to gain unauthorized access and provide actionable recommendations to mitigate each risk.
Mainframe systems are often viewed as being more secure than other types of systems because they are difficult to access and require specialized knowledge to work with. Mainframe penetration testing can help to identify these vulnerabilities so they can be addressed before an attacker has a chance to exploit them.
Why Conduct a Mainframe Pentest?
Conducting penetration of your mainframe test provides invaluable insights into the potential security risks your organization may face from modern threats. Here is what you will get after conducting a project with our team:
Validate your existing security controls
Our mainframe penetration tests will help validate the effectiveness of your existing security controls in preventing and detecting attacks. By simulating an attacker, our experts will identify gaps in your defenses and provide remediation measures to improve your ability to prevent cyberattacks.
Understand the potential impact of an attack on your mainframe
Our tests will identify and measure vulnerabilities that could be exploited to gain access to sensitive data or systems, compromise operations, or affect availability. By understanding exactly what could happen during an attack, organizations can prioritize their security efforts and allocate resources effectively.
Identify & fix all existing vulnerabilities
Our services will help you identify all existing vulnerabilities in your mainframe infrastructure. This will help you prioritize remediation efforts and reduce your overall risk exposure.
Improve your mainframe security
Our services will provide detailed information on how an attacker can breach your mainframe infrastructure, what data or systems they could target and how to protect them. With this information, our team will provide you with custom prioritized recommendations to improve your security posture and protect your mainframe against potential intrusions.
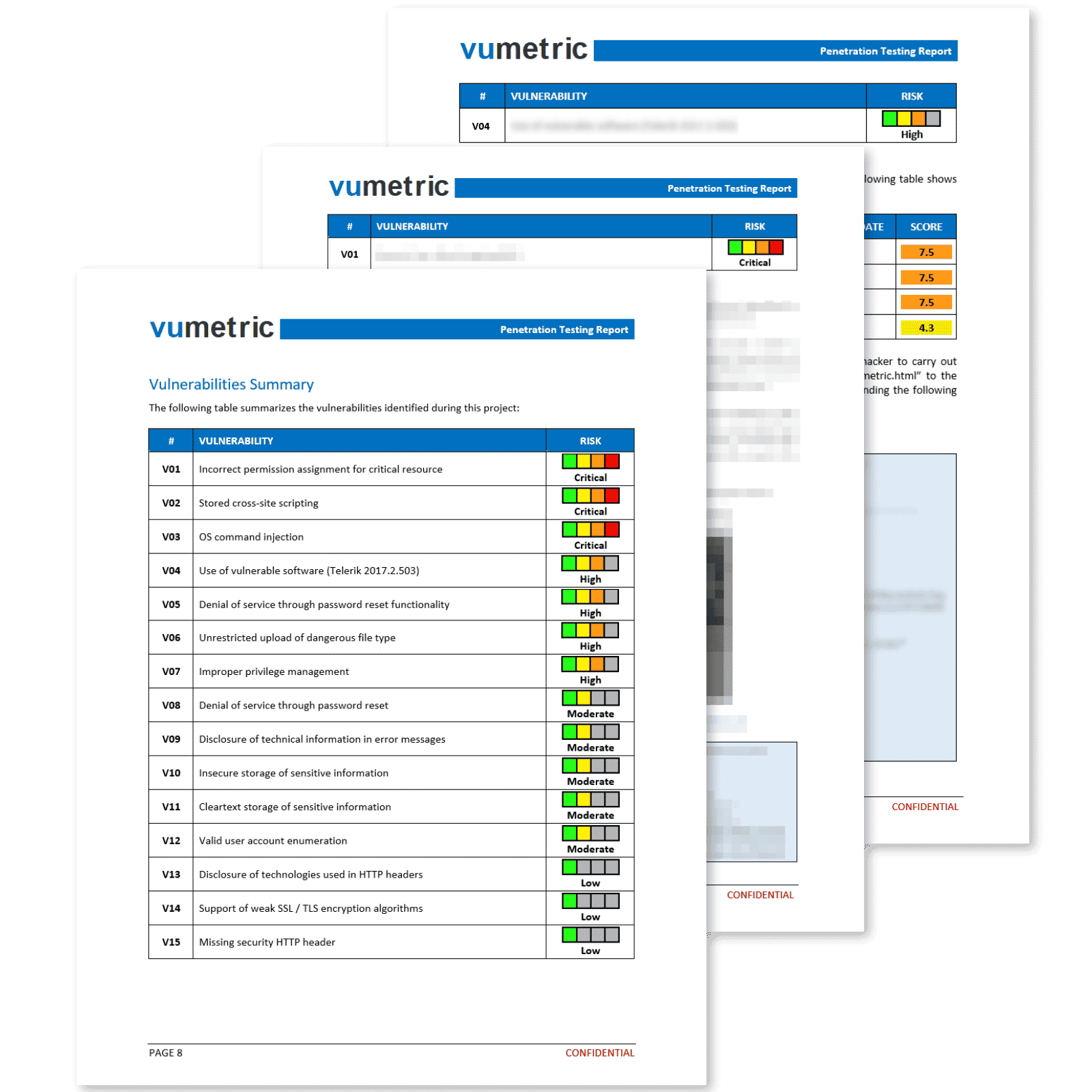
Common Cybersecurity Risks & Vulnerabilities Identified
Privilege escalation
A vulnerability that enables an attacker to elevate their access level within a system, potentially leading to unauthorized control over sensitive data, system configurations, and critical operations, as well as the ability to create or modify user accounts.
Weak or default passwords
A vulnerability stemming from the use of easily guessable or factory-set passwords, which can be exploited by attackers to gain unauthorized access to systems, potentially leading to data theft, unauthorized changes, or other malicious activities.
Insecure configurations
Vulnerabilities caused by improper or suboptimal system settings that can be exploited by attackers to bypass security mechanisms, access sensitive data, or disrupt system operations, potentially leading to data breaches or system downtime.
Library access vulnerability
Security flaws that allow unauthorized access to critical system libraries, potentially enabling attackers to modify, delete, or execute code, leading to data corruption, system instability, or other malicious activities.
Public dataset vulnerability
Vulnerabilities related to public datasets that can be exploited by attackers to access or manipulate sensitive information, potentially leading to data breaches, unauthorized modifications, or other harmful consequences.
Inadequate access controls
Security weaknesses that result from insufficient restrictions on user access within a system, potentially allowing attackers to perform unauthorized actions or access sensitive data, leading to data breaches, unauthorized changes, or other malicious activities.
When Should You Perform a Mainframe Penetration Test?
- Annually as part of a proactive security strategy
- After major system updates or infrastructure changes
- Following the addition of new sensitive features
- In response to new threats or vulnerabilities discovered within your industry
- Prior to an M&A transaction or other major business event
- To maintain compliance with industry-specific regulations or standards
DID YOU KNOW?
“ 95% of companies say they're concerned about the potential of customer data breaches on their mainframe ”
Ready to Conduct a Mainframe Penetration Test?
The Main Benefits of Conducting Mainframe Penetration Testing?
Better understand your mainframe security posture
Prevent attacks on your mainframe and internal infrastructure
Prioritize and plan future security investments
Measure resilience to ransomware attacks
Identify and fix technical vulnerabilities
Frequently Asked Questions
Couldn’t find the information you were looking for? Ask an expert directly.
Mainframe penetration testing is designed to identify and fix vulnerabilities within mainframe systems, ensuring the security of your mission-critical infrastructure. This helps protect against unauthorized access, data breaches, and other cyber threats.
The process begins with an initial assessment of your mainframe environment. Our certified experts then use various attack techniques to simulate real-world threats and identify vulnerabilities. Once vulnerabilities are found, we provide actionable recommendations to mitigate each risk.
In order to ensure a comprehensive assessment, documentation on your mainframe architecture and network topology may be required. Additionally, a solution for our team to remotely access the systems will have to be deployed. Any access requirements will be determined and agreed on in a pre-testing call with your team.
Yes, you’ll need to grant our experts the necessary access and permissions to conduct the mainframe penetration testing remotely in an effective manner. This includes access to the mainframe system, relevant credentials, and any required permissions.
Our mainframe penetration testing services are designed to minimize disruption to your organization’s operations. We work closely with your team to schedule testing during periods of low system activity and ensure that any potential impact on your operations is minimized. Our tests are unnoticeable for the overwhelming majority of our clients.
Mainframe penetration testing is a crucial component of a comprehensive and advanced cybersecurity strategy. By identifying and addressing vulnerabilities in your mainframe system, you can strengthen your organization’s overall security posture and ensure the protection of your most critical infrastructure.