OUR OFFICE 365 SECURITY AUDIT SERVICES
What is an Office 365 Security Audit?
Office 365 security audits assess tenant configurations of any O365 services used by an organization to ensure they cannot be exploited and compromised by hackers to move laterally within the infrastructure and perform further malicious acts. It provides an overview of the environment’s security risks to help organizations better understand their current cybersecurity posture and provides a prioritized roadmap to mitigate any identified risks.
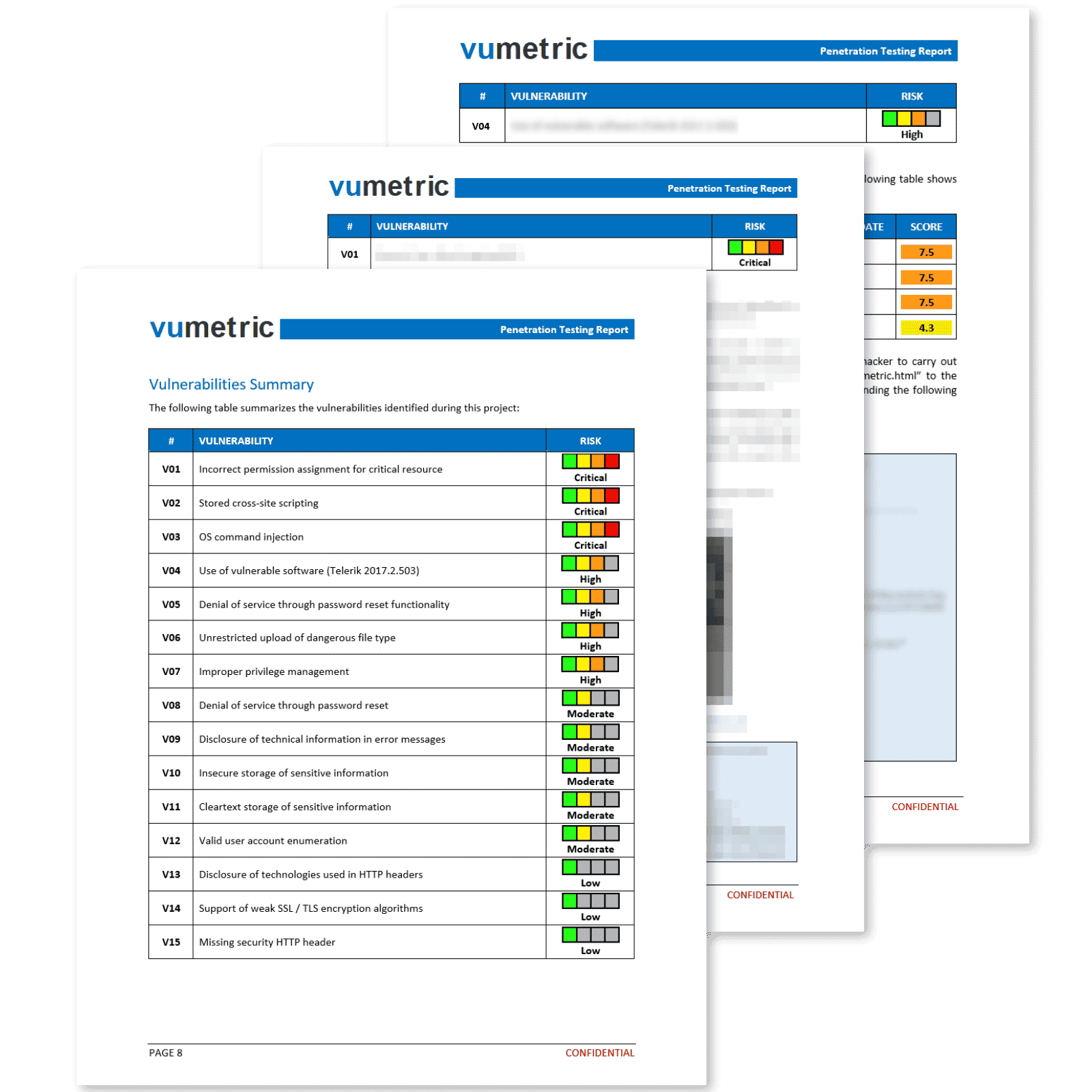
VULNERABILITIES
What our Office 365 Security Audit Cover
In order to maximize the identified risks and to properly secure your tenant, our assessment focuses on (but is not limited to) the following areas:
Access Control
Security Policies

Email Security
Data Security
Monitoring Logs

Security Configurations
BENEFITS
Why Review Your Office 365 Security?
Office 365 audits, generally complementary to external penetration testing, provide real-world examples of attacks your tenant is vulnerable to. This assessment is particularly cost-effective, as specialists gain direct access to your configurations to better understand the risks you are confronted with.
Protect your infrastructure from ransomware attacks
Protect your users from phishing attempts
Secure sensitive data from unauthorized access
Secure your emails from malware & BEC attacks
Validate the security of existing policies and configurations
Protect your infrastructure from ransomware attacks