What is Wireless Penetration Testing?
Wireless Penetration Testing is an assessment that identifies vulnerabilities within wireless access points, such as WiFi networks and wireless devices using the same techniques as hackers to breach your infrastructure.
Our Wireless Testing is designed to fix any security flaw within WLANs and connected equipment that would allow attackers to gain unauthorized access and compromise sensitive information.
Wireless testing can help organizations identify and fix weaknesses in their wireless networks before attackers have a chance to exploit them.
Why Conduct a Wireless Pentest?
Conducting a wireless network penetration test provides invaluable insights into the security risks of your WiFi network and devices. Here is what you will get after conducting a project with our team:
Validate your existing security controls and network segmentation
Our tests will test the effectiveness of your existing security controls in preventing and detecting attacks and help validate the proper segmentation of your wireless network. By simulating an attacker, our experts will identify gaps in your defenses and provide remediation measures to improve your ability to prevent cyberattacks.
Understand the potential impact of an attack on your WiFi networks and devices
Our external penetration tests will identify and measure vulnerabilities that could be exploited to gain access to sensitive data or systems, compromise operations, or damage your reputation. By understanding exactly what could happen during an attack, organizations can prioritize their security efforts and allocate resources effectively.
Identify & fix all existing vulnerabilities
Our wireless pentests will help you identify all existing vulnerabilities in your wireless infrastructure, including critical vulnerabilities that could be exploited by an attacker to move laterally to your internal network or intercept sensitive user data. This will help you prioritize remediation efforts and reduce your overall risk exposure.
Improve your wireless network security
Our services will provide detailed information on how an attacker can breach your wireless network, what data or systems they could target and how to protect them. With this information, our team will provide you with tailored recommendations to improve your security posture and protect against potential threats.
Comply with regulatory requirements
Many regulatory frameworks require wireless penetration testing as part of their compliance requirements. Our tests will help ensure that your organization meets these requirements efficiently and avoids potential penalties for non-compliance.
Our Wireless Penetration Testing Services
Our wireless penetration tests allow you to determine the impact of an attack targeting your wireless network and provide actionable recommendations to fix any identified vulnerability.
Wireless penetration testing can help to mitigate these risks by identifying weaknesses and vulnerabilities in the system. By conducting regular pen tests, businesses can ensure that their wireless networks are secure and protected from potential threats.
Network Segmentation
Penetration Testing
Test your network's segmentation.
WiFi Network
Penetration Testing
Test your WLAN networks.
Wireless Devices
Penetration Testing
Test your connected equipment.
Common Cybersecurity Risks & Vulnerabilities Identified
There are many common wireless network vulnerabilities that can leave your data and devices unprotected, as WiFi networks are generally less secure than traditional wired networks. The following vulnerabilities are the most commonly found within wireless networks:
Rogue access points
A vulnerability that allows an attacker to setup an unauthorized wireless access point to intercept and capture sensitive information.
Vulnerable encryption
Vulnerable encryption can allow attackers to intercept and capture sensitive information that is transmitted by users over a wireless network.
Security policy flaws
A vulnerability that allows attackers to bypass security controls and gain access to a network to launch further attacks.
Weak passwords
Attackers can exploit weak passwords to gain access to sensitive information or launch further attacks on the network.
Misconfigured routers
Misconfigured routers provide an entry point for hackers to gain access to sensitive information or launch further attacks on the network.
Unsecured guest networks
Unsecured guest networks provide attackers with a pathway to gain unauthorized access to infiltrate a wireless network.
When Should You Perform a Wireless Penetration Test?
- Before deploying a new system or application to the internet
- After making significant changes to the network or infrastructure
- Prior to a compliance audit or assessment, such as SOC 2 or PCI-DSS
- Following a security breach or incident
- Annually as part of a proactive security strategy
- Prior to an M&A transaction or other major business event
Need to Conduct a Penetration Test of Your Wireless Network?
The Main Benefits of Testing The Security of Your Wireless Network
Wireless networks have become such an important vector of attack for hackers that various standards, such as PCI-DSS or SOC 2, require a yearly wireless penetration test to remain compliant.
No matter what type of wireless network is used by your organization, it’s important to perform a regular assessment to stay protected.
Confirm proper network segmentation to ensure guest networks are isolated from critical infrastructures.
Identify & fix opportunities for hackers to move laterally through your network by elevating privileges.
Understand the business impacts of wireless infrastructure vulnerabilities.
Frequently Asked Questions
Couldn’t find the information you were looking for? Ask an expert directly.
Wireless network penetration testing is essential for organizations to ensure the security of their wireless networks and connected devices. Conducting such tests helps identify potential vulnerabilities and weaknesses, address them, and prevent cyberattacks. Wireless penetration testing is required by various compliance standards, and it helps organizations gain a deeper understanding of their cybersecurity posture.
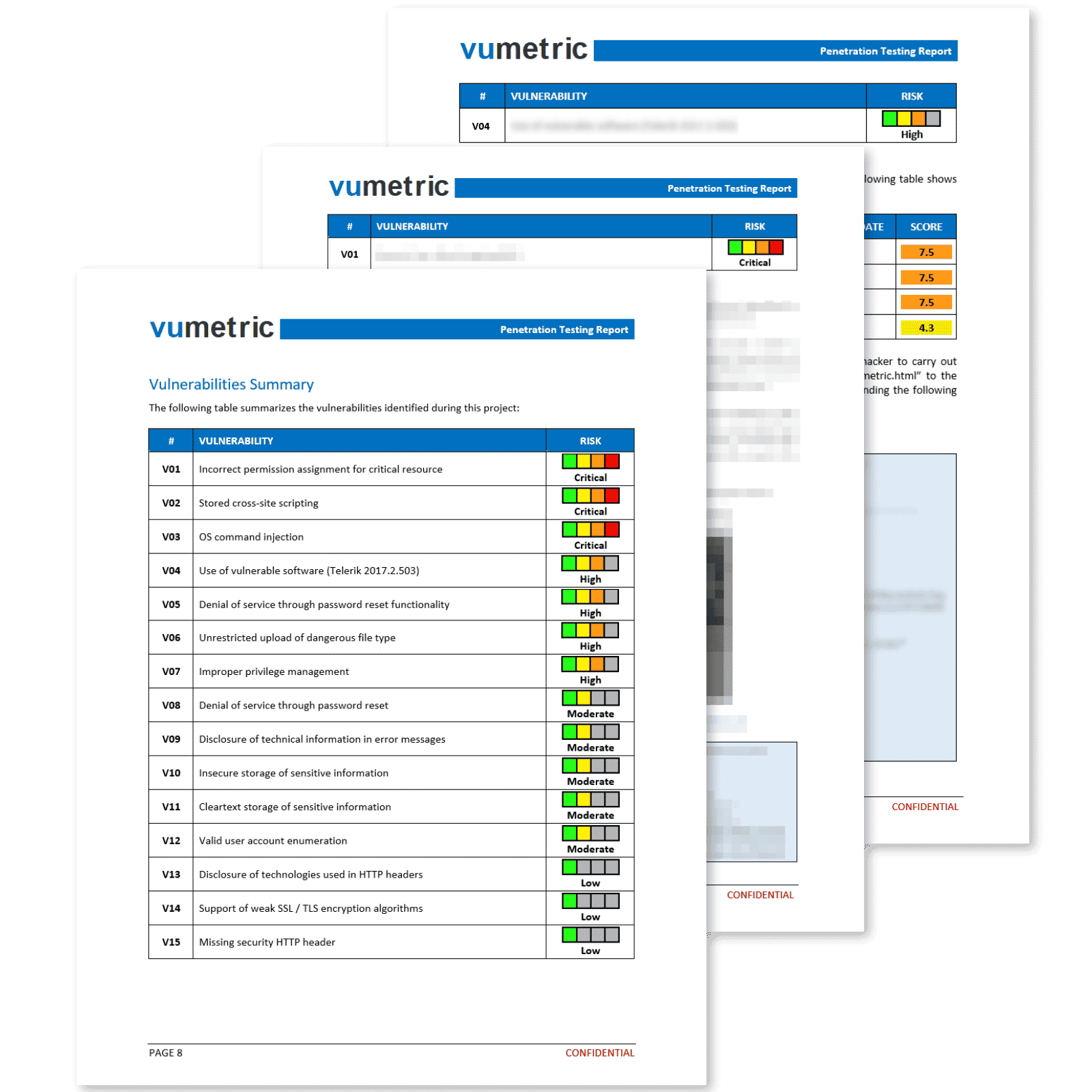
Wireless penetration testing involves a process of identifying vulnerabilities in wireless networks and connected devices, using various techniques to gain unauthorized access, escalate privileges, and move laterally through the network to access sensitive data or critical systems. After the testing, the testers provide a detailed report outlining the vulnerabilities found and the recommended remediation steps to address them.
The requirements to get started with Wireless Network Penetration Testing include deploying a virtual access to the wireless network and connected devices, ensuring that the test will not interfere with business operations, and having a clear understanding of the scope of the assessment before contacting a provider.
Yes, you will need to provide access to the wireless network and connected devices for the tests to be conducted. This may include providing login credentials or access to physical devices. Our experts will discuss any access requirements with your team and offer multiple solutions to determine the best approach in a pre-launch call.
Wireless Network Penetration Testing is an essential part of a company’s overall cybersecurity strategy. It helps identify potential vulnerabilities in wireless network infrastructure, often a weak point for organization, which can be proactively addressed to prevent potential cyberattacks.
Yes, our services helps several companies every year to meet compliance requirements by identifying potential vulnerabilities in their wireless network infrastructure. Once remediation testing is completed, we provide an official attestation confirming that vulnerabilities have been remediated, helping organizations meet compliance requirements efficiently.